Obama Leak “Witch Hunt”: The Computer Intrusions

Above image: Journalist SharylAttkisson testifies to Congress about the proposed “SHIELD” law to protect reporters from revealing confidential sources, July 2018
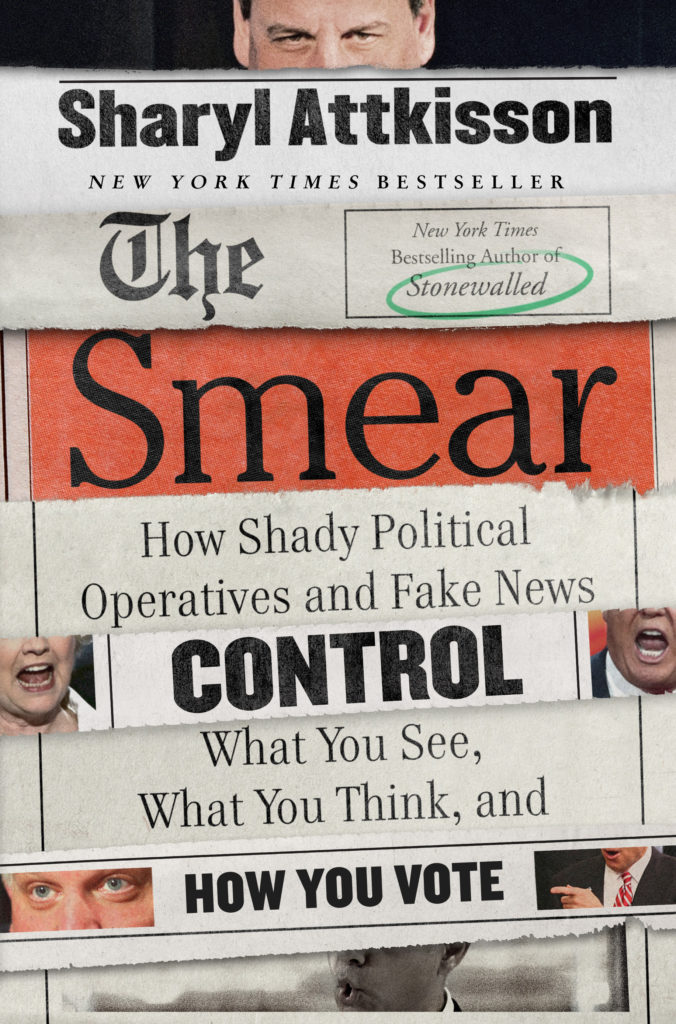
The following is the 11th in a series of excerpts from my New York Times bestseller “Stonewalled,” which recounts the government intrusions of my computers. More excerpts to follow.
I appreciate their consideration, but I don’t think they’ll find anything.
“What’s the point?” I ask.
“You never know, you might be surprised at what turns up. And it’s no trouble to look,” says one.
Between the two of them, they check the walls, the telephones. Lamps, bookshelves. They climb into the attic, where the Verizon man once lurked. They disassemble my electric power strips, examine the alarm system, and sweep the inside and outside of my car. Nothing.
The truth is, I’ve given up on the idea of privacy for the moment. Those who possess the skills to do what they’ve already done can pretty easily penetrate most any computer or device, most anytime, most anyplace. One source explains to me that Microsoft works on coding with the government so that anti-malware programs view the government’s spyware as something friendly that belongs in the Microsoft environment. I belong here, the intruder tells the virus scanner. Move along, nothing to see, you amateurs. I can switch out phones, put a Band-Aid over the camera in my computer, and run debugging programs all day long. For those who have the toys and technology, defeating my defenses is child’s play.
On May 6, 2013, I make contact with an excellent source who has crucial information: the name of the person responsible for my computer intrusions. He provides me the name and I recognize it. I’m not surprised. It strikes me as desperate and cowardly that those responsible would resort to these tactics. That’s all I can say about that for now.
Support the Attkisson v. DOJ/FBI Fourth Amendment Litigation Fund to fight the government computer intrusions
The inspector general’s office checks in and gives me a bit of infor- mation. It’s the same thing Number One told me in January: there’s no PATRIOT Act order on me. The IG official also says the FBI denies having anything to do with my situation. Naturally, I’m dubious. I wonder who at the FBI was asked, what words they used in their denial, and was any of this put in writing. I suggest to the IG official that he might not be getting the whole story. He wants to know if my sources will speak with his office. I approach Number One.
“Frankly, I’m not comfortable,” he tells me. “The IG works for the people who did this to you.”
Inspectors general are supposed to be independent watchdogs of their agencies, and the Justice Department IG has a good reputation. But there can be an element of political influence even in some of the best IG offices. Number One’s been around the block. He doesn’t trust the IG. He says I shouldn’t, either.
A diverse group of Constitutional free press and privacy advocates is supporting Attkisson v. Dept. of Justice/FBI to fight the government computer intrusions. Click here to support.
It’s with great interest that I retrospectively view an interesting publication on WikiLeaks to which a contact directs my attention. On February 27, 2012, WikiLeaks began publishing five million emails purported to be from the Texas-headquartered “global intelligence” company Stratfor. One document of particular interest is dated September 2010 and is titled, “Obama Leak Investigations.”
“Brennan is behind the witch hunts of investigative journalists learning information from inside the beltway sources,” it says. “There is a specific tasker from the [White House] to go after anyone print- ing materials negative to the Obama agenda (oh my). Even the FBI is shocked.”
Stratfor email, Sept. 2010 via WikiLeaks
All of this tees up the global news that’s about to break revealing the Obama administration’s surveillance of reporters—and the general public.
Actual email text follows:
Obama Leak Investigations (internal use only—pls do not forward)
Released on 2012-09-10 00:00 GMT Email-ID: 1210665
Date: 2010-09-21 21:38:37
From: [email protected]
To: [email protected]
Brennan is behind the witch hunts of investigative journalists learning information from inside the beltway sources.
Note—There is specific tasker from the WH to go after anyone printing materials negative to the Obama agenda (oh my.) Even the FBI is shocked. The Wonder Boys must be in meltdown mode. . . .
To Be Continued…
Read excerpt #1 here: The Computer Intrusions: Up at Night
#2: Big Brother: First Warnings
#3: The Computer Intrusions: Disappearing Act
#4: The Incredible, Elusive “Verizon Man”
#5: I Spy: The Government’s Secrets
#6: Computer Intrusions: The Discovery
#7: Notifying CBS About the Government Computer Intrusions
#8: The MCALLEN Case: Computer Intrusion Confirmed
#10: Revelations in the Government Computer Intrusion


![]()
Original source: https://sharylattkisson.com/2018/12/27/obama-leak-witch-hunt-the-computer-intrusions/
See comments at original source: https://sharylattkisson.com/2018/12/27/obama-leak-witch-hunt-the-computer-intrusions/#comments